The Zero-Trust Data Management Platform
Extract data securely from private databases, automate PII masking, and map your downstream dependencies. Saddle Data combines the security of an outbound-only agent with enterprise-grade data governance.
Start Building for Free
Stop Playing Whack-a-Mole with Broken Pipelines
Centralized Data Asset Registry
Decouple schemas from individual syncs. Register a database as a reusable Data Asset, update it once, and Saddle Data dynamically handles the routing everywhere.
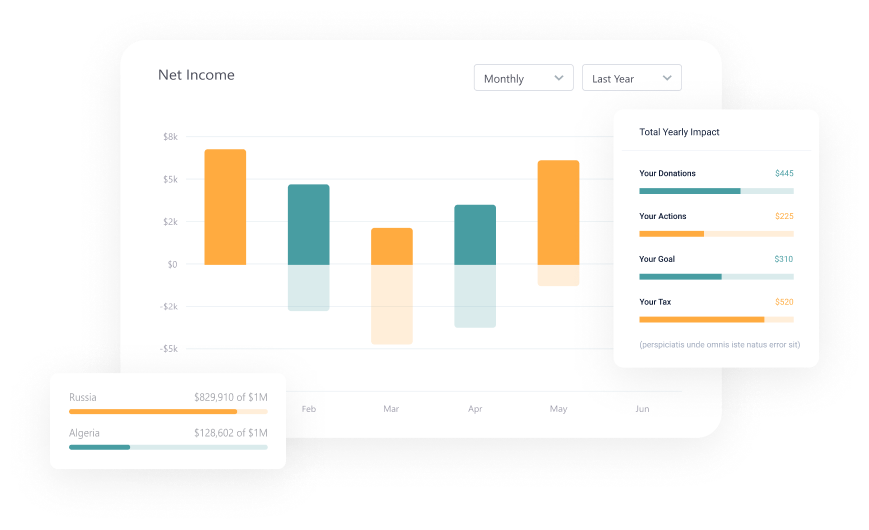
Global Impact Analysis (Blast Radius)
See the future before it breaks. Instantly view a visual dependency graph showing exactly which downstream dashboards will fail if you alter a source table.
Automated PII Enforcement
Zero-trust compliance on autopilot. Tag a column as sensitive once, and we automatically inject masking/hashing transformations into every flow that uses it.
The Schema Time Machine
Data drifts. We track it. Get an automated, AI-generated, human-readable audit log of exactly when and how your upstream schemas changed.
In-Flight AI Embeddings
Feed your RAG applications natively. Automatically transform raw text into AI vector embeddings mid-stream using Google Gemini or OpenAI.
Secure Remote Agents
Never open an inbound firewall port again. Run a single Go binary inside your VPC to extract data securely via persistent outbound-only WebSockets.
Enterprise Governance, Built for SREs.
Legacy ETL hides schemas inside individual jobs, meaning a single upstream change can break 50 downstream dashboards. Saddle Data treats your data as a centralized asset. Map your dependencies visually, enforce security policies globally, and never rely on human memory for InfoSec compliance again.
How It Works: Secure Hybrid ELT
**1. Secure Extraction:** Your Remote Agent pulls data from private databases using an outbound-only connection. **2. Global Policy Enforcement:** Sensitive columns are automatically hashed or masked based on your Data Asset Registry rules. **3. Intelligent Loading:** We perform fast Incremental Upserts into analytical warehouses or Vector DBs. **4. Blast Radius Mapping:** Monitor the entire multi-step process and track downstream dependencies through a single visual DAG.

Ready to secure your data pipelines?
Deploy your first remote agent and establish a secure, governed data flow in under 5 minutes.
Sign Up for Free